Viruses … Viruses … Everywhere (Part 2 of 3)
Warning 1: Part 2 is marginally more technical than Part 1. However I have found a way to inject a picture of a cute female and another of a (cute?) dog. So those readers that are totally put off by overly technical blogs can continue reading with a reasonable degree of safety if they are so inclined.
Warning 2: This blog is longer than my self imposed 500 word limit. It just creeps into 1,000 words.
In Part 1 I set the stage for how a nice, well-behaved, much-loved and cared for home computer can become almost completely useless due to a relatively sudden and unexpected overload of computer malware, other associated viruses, and general nasties. Notice in the picture shown here how happy the seriously cute niece (SCN) is as she works away on her faithful and obedient home computer (and yes, I understand she can touch-type with 100 percent accuracy using one hand while smiling for the camera).

So, at this point, all is good.
But then comes the phone call: “Uncle Barry, there is something wrong with my computer. It is going really slow and I cannot use Internet Explorer at all”. Okay. That might not be exactly what she said, but you get the general idea. The computer is in a bad way. It is screaming out for help. This phone call usually ends with “and I haven’t done anything. Honest. It just happened all by itself”.
So we get the computer around to my ‘workshop’, or what my wife jokingly refers to as “a complete mess of an office” (at least I think she is joking). When I start up SCN’s computer the first thing I notice is that the Trend Micro Systems anti-virus agent is not showing in the agent and services part of the Start Bar. Also, when I try to go to Control Panel I get an error. And finally, when I put Super Anti Spyware on a USB memory stick and try to install it I find I can’t; these all being classic indications that one or more viruses now have control of this PC.
What typically happens is that one reasonably clever ‘super’ (RCS) virus manages to get installed. This happens because:
- the anti-virus scanner on the computer is not tuned in to what this RCS virus looks or 'smells' like,
- the computer does not have a functioning up-to-date anti-virus scanner installed and working, or
- the computer user actually—unknowingly—gave either the virus scanner or the operating system, or both, approval to install the RCS virus even though it was detected and an alert was issued.
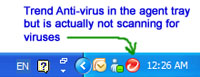 Which-ever of the above occurred; all it takes is for that one RCS virus to get installed. Once that first bit of high-tech malware makes it past the gates then it goes to work kicking down the barriers so that more and more bits and pieces of malware can join it. In a matter of days your computer is crawling with every type of malware the RCS virus knows about because your virus scanner has been compromised (which is techo-code for “is now completely useless”). Even if it is still showing on the Start Menu in the agent tray your virus scanner is most likely disabled or has been otherwise rendered ineffective.
Which-ever of the above occurred; all it takes is for that one RCS virus to get installed. Once that first bit of high-tech malware makes it past the gates then it goes to work kicking down the barriers so that more and more bits and pieces of malware can join it. In a matter of days your computer is crawling with every type of malware the RCS virus knows about because your virus scanner has been compromised (which is techo-code for “is now completely useless”). Even if it is still showing on the Start Menu in the agent tray your virus scanner is most likely disabled or has been otherwise rendered ineffective.
So now there are two possible outcomes:
- Possible Outcome 1: The malware can be found and treated (quarantined or eradicated) such that the operating system will still boot up and the PC will still function okay.
- Possible Outcome 2: Finding and treating the malware will destroy the operating system and it will not longer either boot up, or if it boots up, it will not function.
Usually when someone brings me a computer infected with malware/viruses and I get to this point I call up Dr. Mike. Mike has been fighting with viruses (human and computer) for some time. He knows all their crafty little tricks—all the little nooks and crannies they crawl into. He has built up a collection of tools to hunt them down and dig them out (see, I avoided saying "root them out").
Dr. Mike’s approach follows a tried and true method developed and refined over years of saving badly infected computers. The infected hard disk, which contains the operating system and usually the bulk of the user’s files, will be surgically removed from its computer. It will then been transplanted (er, installed) into another computer as a secondary disk, and only as a data disk (i.e. not as a bootable disk). Then it will be tirelessly scanned and re-scanned by Dr. Mike using a number of anti-virus scanners and special purpose malware scanners kept handy for just this purpose. The plan here is to find all malware and viruses buried away on the disk and do whatever is needed to be done to make them ineffective.
This process can take some time to complete. Depending on factors such as the size of the infected hard disk, whether the user has a trusted and working backup of all data on the hard disk, or how much data is stored on the hard disk, it can take several hours just to complete a single scanning pass of the complete disk. For this reason it is sometimes good to have a friendly dog lying around to keep you company. Oh. As it happens Dr. Mike is even prepared for this. Meet Mike's dog Toby, the false maltalier.
It seems that this is not what a maltalier dog should look like, hence the term “false maltalier”. Also, even though I am sure his nose works as good as a real maltalier, he seems to be absolutely useless when it comes to 'sniffing out' a virus on a computer's hard disk. But I am not sure bona-fide maltalier’s are any good at that anyway. Maybe it is just a matter of more training? On the upside he does provide a little light relief when the virus hunting gets too intense. We often play tug-o-war with him, or, a spot of 'careful you don't run over the dog's tail with the chair' (always a popular game when virus hunting).
So that is it for Part 2. In Part 3 (the final Part) I will tell you what we ended up finding and then deciding to do, and if you are really lucky I might be able to squeeze in another SCN picture—assuming I don’t get into trouble for putting in the one that is in this post.
Barry.

